Synthetic identity fraud is the fastest-growing form of fraud in the world, yet far too many companies and businesses vulnerable to synthetic identity theft are not taking adequate precautions to prevent it. Indeed, it’s estimated that standard customer onboarding processes fail to detect synthetic identities 95% of the time, resulting in an average loss of about $15,000.
The key to detecting and preventing synthetic identity fraud before it happens is understanding how synthetic identities differ from real identities and employing a software tool capable of distinguishing between the two. Thomson Reuters CLEAR ID Confirm and AU10TIX have partnered to create a solution that can reliably verify identities in seconds and is almost impossible to fool.
Real vs. Synthetic Identities
One way criminals create synthetic identities is by creating a fake persona and attaching it to a legitimate Social Security Number stolen from someone else, many times a minor or a deceased person. But in most cases, the fakery doesn’t go very far or deep. Synthetic identities typically contain just enough information to satisfy a quick know-your-customer (KYC) check: a fake name, address, contact information, and driver’s license, plus a few bogus social media feeds to create the illusion of a real person or business—but not much more.
For purposes of detection, the difference between a synthetic identity and a real person is that real people tend to have a much more complex and nuanced digital presence. They often have multiple addresses and phone numbers attached to their name (from moving), and their digital trail is scattered with evidence of actual living: e.g., DMV records, parking tickets, marriage licenses, divorce documents, news mentions, and an extended network of professional and personal contacts. Real people also have different behavior and purchasing patterns, and they establish these patterns over a long period of time.
So, to distinguish between a synthetic identity and a real person during the onboarding process using a software tool, the tool needs to be able to quickly compare information submitted by the applicant to supporting records online. It also needs to be able to flag any anomalous behavior patterns, inconsistencies, or missing data that may appear suspicious or out of character.
CLEAR ID Confirm + AU10TX
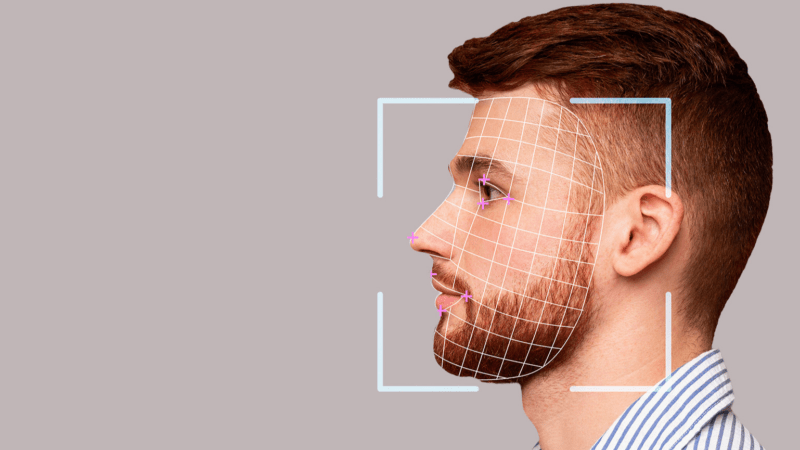
The combination of CLEAR ID Confirm and AU10TIX verifies identities by using a multi-step process to compare the data submitted by an applicant to relevant online records, documents, biometric markers (e.g., photos), sanctions lists, and other publicly available information. The system also uses data analytics to identify anomalous behavior patterns, as well as proprietary technology to detect forged driver’s licenses, passports, and signatures.
Using these tools, synthetic identities can be spotted in a matter of seconds.
For example, to detect a synthetic identity before it can do any harm, the customer verification process would look something like this:
1— CLEAR ID Confirm software would conduct broad public records searches to confirm that the person or business applying really exists, then provide an instant risk assessment, flagging any applicant with errors or inconsistencies in their public data profile. It would also screen for sanctions violations and other evidence of possible fraud.
2— The AU10TIX solution would then validate that the person is the person they say they are. The potential customer is asked to provide their name and contact information, a government-issued ID (e.g., driver’s license, passport), and a selfie photo for comparison.
3—If AU10TIX identified a potential anomaly, the flagged file would undergo a rigorous follow-up assessment to determine the validity of an applicant’s information, starting with a proprietary Identity Document Verification (IDV) review that can identify forged licenses, passports, and signatures in more than 200 languages.
4—A secondary IDV scan capable of detecting even the most sophisticated ID forgeries would be run, along with a proprietary form of adaptive data analytics that assesses identity risk based on suspicious or anomalous behavior patterns.
5—Using the selfie taken at sign-up, scanning would perform a face-to-face comparison with ID documents to ensure a match and conduct a face liveness test to ensure that the applicant is a real person, not a digital fake.
6—For further clarification that a person or business is real, the program would scan global consumer and government databases for supporting documentation.
7—For documents that can’t be verified or recognized through initial scans, a manual document review from a trained professional can be requested.
Using CLEAR ID Confirm + AU10TX automatic risk scoring flags any person or business that may be a synthetic identity. The system also alerts the user to any entity associated with fraud, money laundering, or other criminal activity, and can provide ongoing monitoring of accounts to ensure security.
Pro-active account protection
Given that most synthetic identities are NOT detected by outdated manual processes during the customer onboarding process, and that criminals themselves are becoming more technologically sophisticated by the day, using equally sophisticated technology to stop synthetic identity fraudsters before they strike is the only practical way to protect vulnerable organizations from future attacks.
Indeed, synthetic identity fraud and other cybercrimes may be on the rise, but there is no reason why financial institutions and other frequently targeted businesses must wait until a crime has been committed before they act. Instead, they can take a proactive approach and use CLEAR ID Confirm + AU10TX to ensure that their onboarding process is as thorough as it is foolproof.
____________________________________________________________________________
Thomson Reuters is not a consumer reporting agency and none of its services or the data contained therein constitute a ‘consumer report’ as such term is defined in the Federal Fair Credit Reporting Act (FCRA), 15 U.S.C. sec. 1681 et seq. The data provided to you may not be used as a factor in consumer debt collection decisioning, establishing a consumer’s eligibility for credit, insurance, employment, government benefits, or housing, or for any other purpose authorized under the FCRA. By accessing one of our services, you agree not to use the service or data for any purpose authorized under the FCRA or in relation to taking an adverse action relating to a consumer application.